Agentic AI functions symbolize a big improvement in enterprise automation, the place clever brokers autonomously execute advanced workflows, entry delicate datasets, and make real-time choices throughout your group’s infrastructure. Amazon Bedrock AgentCore accelerates enterprise AI transformation by offering totally managed providers that take away infrastructure complexity, preserve session isolation, and allow seamless integration with enterprise instruments so organizations can deploy reliable AI brokers at scale. AgentCore Gateway, a modular service beneath AgentCore, simplifies integration by securely reworking APIs, AWS Lambda capabilities, and providers into Model Context Protocol (MCP)-compatible instruments and making them obtainable to brokers by way of a unified endpoint, with built-in authentication and serverless infrastructure that minimizes operational overhead.
In manufacturing environments, AI brokers are usually deployed inside digital non-public clouds (VPCs) to take care of safe, remoted community entry and to fulfill enterprise safety and compliance necessities. Amazon Internet Providers (AWS) interface VPC endpoints can improve agentic AI safety by creating non-public connections between VPC-hosted brokers and AgentCore Gateway, maintaining delicate communications throughout the safe infrastructure of AWS. These endpoints use devoted community interfaces with non-public IP addresses to ship diminished latency and superior efficiency by way of direct connectivity. Moreover, VPC interface endpoints provide granular entry management by way of endpoint insurance policies, streamline operations by avoiding proxy server administration, cut back knowledge switch prices, and set up the safe basis that autonomous AI methods require when processing confidential knowledge in regulated environments at enterprise scale.
On this submit, we display learn how to entry AgentCore Gateway by way of a VPC interface endpoint from an Amazon Elastic Compute Cloud (Amazon EC2) occasion in a VPC. We additionally present learn how to configure your VPC endpoint coverage to supply safe entry to the AgentCore Gateway whereas sustaining the precept of least privilege entry.
Structure overview
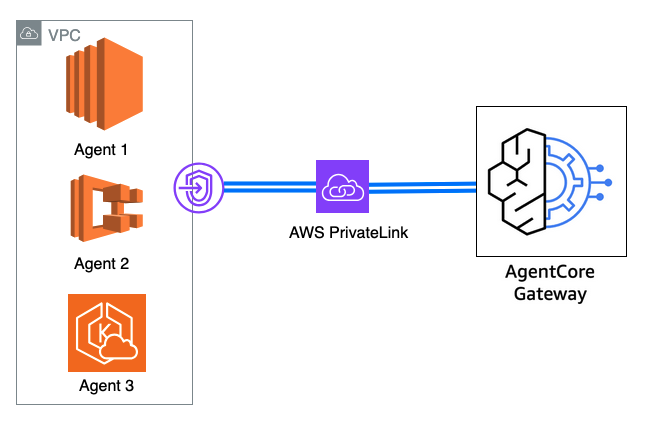
This structure diagram illustrates a consumer accessing an software supported by backend brokers deployed throughout varied AWS compute providers, together with EC2 situations, Lambda capabilities, Amazon Elastic Kubernetes Service (Amazon EKS), or Amazon Elastic Container Service (Amazon ECS), all working inside a VPC surroundings. These brokers talk with AgentCore Gateway to find, entry, and invoke exterior instruments and providers which have been reworked into agent-compatible sources, reminiscent of enterprise APIs and Lambda capabilities. In the usual configuration, agent requests to AgentCore Gateway traverse the general public web. By implementing interface VPC endpoints, organizations can route these communications by way of the AWS safe inner community spine as an alternative, delivering vital advantages that may embody enhanced safety, diminished latency, and improved compliance alignment for regulated workloads that require strict community isolation and knowledge safety requirements. The answer follows this workflow:
- AI agent interplay – An agent working throughout the VPC obtains the required inbound authorization from id suppliers, authenticates with Gateway, and sends a tool-use request (invokes the MCP instrument) to the gateway by way of the interface VPC endpoint.
- Gateway processing: Gateway manages OAuth authorization to ensure solely legitimate customers and brokers can entry instruments and sources. The inbound request is allowed by Gateway. Converts agent requests utilizing protocols like Mannequin Context Protocol (MCP) into API requests and Lambda invocations
- Safe entry: The gateway handles credential injection for every instrument, enabling brokers to make use of instruments with completely different authentication necessities seamlessly. It makes use of AgentCore Identification to securely entry backend sources (the targets) on behalf of the agent.
- Goal execution: The gateway knowledge aircraft invokes the goal, which is usually a Lambda operate, an OpenAPI specification, or a Smithy mannequin.
- Monitoring: AgentCore Gateway gives built-in observability and auditing. Moreover, AWS PrivateLink publishes metrics to Amazon CloudWatch for monitoring interface endpoints. You may optionally allow VPC Movement Logs for logging IP visitors to AgentCore Gateway.
Concentrate on the next key issues:
- Non-public and public community communication – The interface VPC endpoint permits safe communication for inbound visitors from brokers to AgentCore Gateway by way of AWS PrivateLink, ensuring this visitors stays throughout the non-public community. Nonetheless, authentication workflows—together with OAuth entry token retrieval and credential alternate processes between brokers and exterior Identification Supplier methods for each inbound and outbound flows—and outbound entry from the gateway to MCP instruments proceed to require web connectivity for establishing safe classes with id methods and exterior sources hosted exterior the AWS surroundings.
- Information aircraft scope – It’s necessary to grasp that, presently, the interface VPC endpoint help is relevant solely to the info aircraft endpoints of your gateway—the runtime endpoints the place your functions work together with agent instruments. To make clear the excellence: though now you can entry your gateway’s runtime endpoint by way of the interface VPC endpoint, the management aircraft operations, reminiscent of creating gateways, managing instruments, and configuring safety settings, should nonetheless be carried out by way of the usual public AgentCore management aircraft endpoint (for instance,
bedrock-agentcore-control.<area>.amazonaws.com)
Conditions
To carry out the answer, you want the next conditions:
- An AWS account with acceptable AWS Identification and Entry Administration (IAM) permissions for VPC and Amazon Elastic Compute Cloud (Amazon EC2) administration
- Current VPC setup with subnet configuration and route tables
- AgentCore Gateway already provisioned and configured in your AWS account
- Fundamental understanding of VPC networking ideas and safety group configurations
Resolution walkthrough
Within the following sections, we display learn how to configure the interface VPC endpoint utilizing the AWS Administration Console and set up safe connectivity from a check EC2 occasion throughout the VPC to AgentCore Gateway.
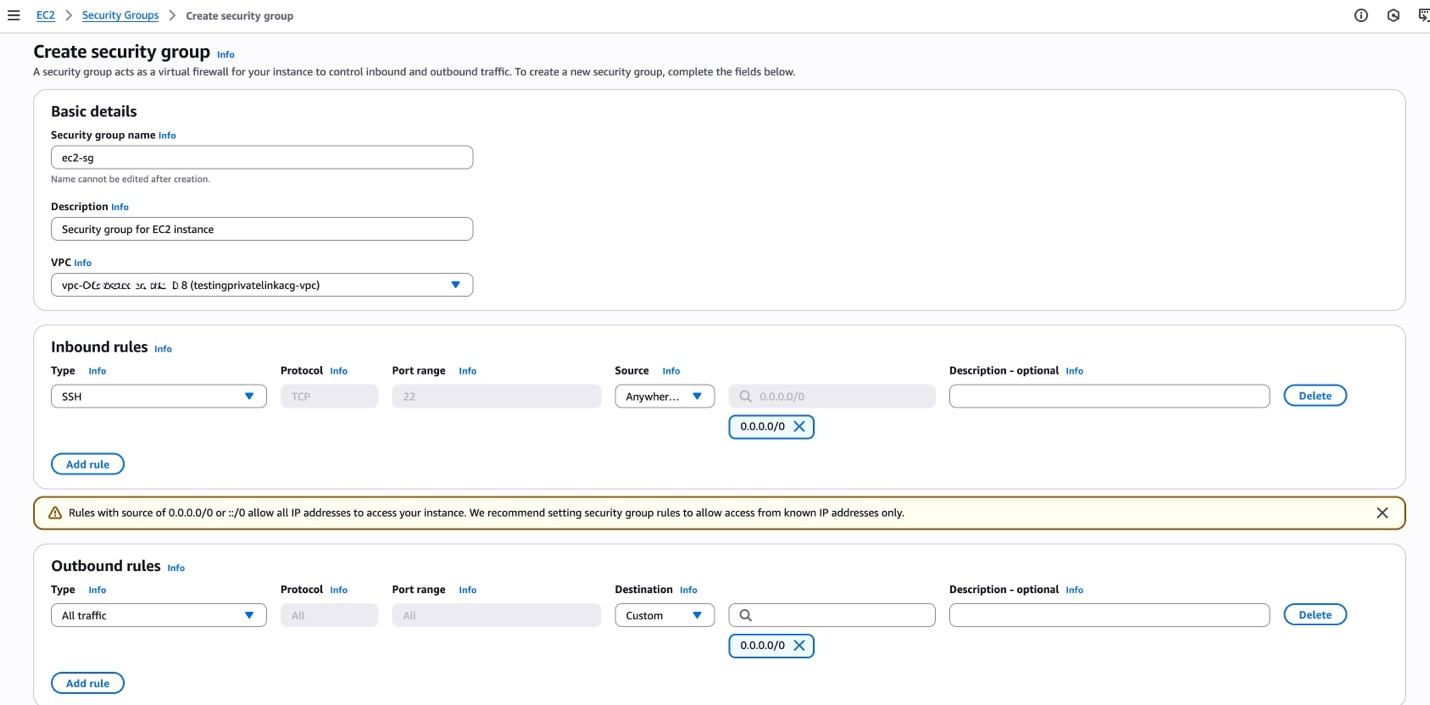
Create a safety group for the EC2 occasion
To create a safety group for the EC2 occasion, comply with these steps, as proven within the following screenshot:
- Navigate to the Amazon EC2 console in your most well-liked AWS Area and select Safety Teams within the navigation pane beneath Community & Safety.
- Select Create safety group.
- For Safety group title, enter a descriptive title reminiscent of
ec2-agent-sg. - For Description, enter a significant description reminiscent of
Safety group for EC2 situations working AI brokers. - For VPC, select your goal VPC.
- Add related Inbound guidelines for the EC2 occasion administration reminiscent of SSH (port 22) out of your administration community or bastion host.
- Go away Outbound guidelines as default (permits all outbound visitors) to ensure brokers can talk with essential providers.
- Select Create safety group.
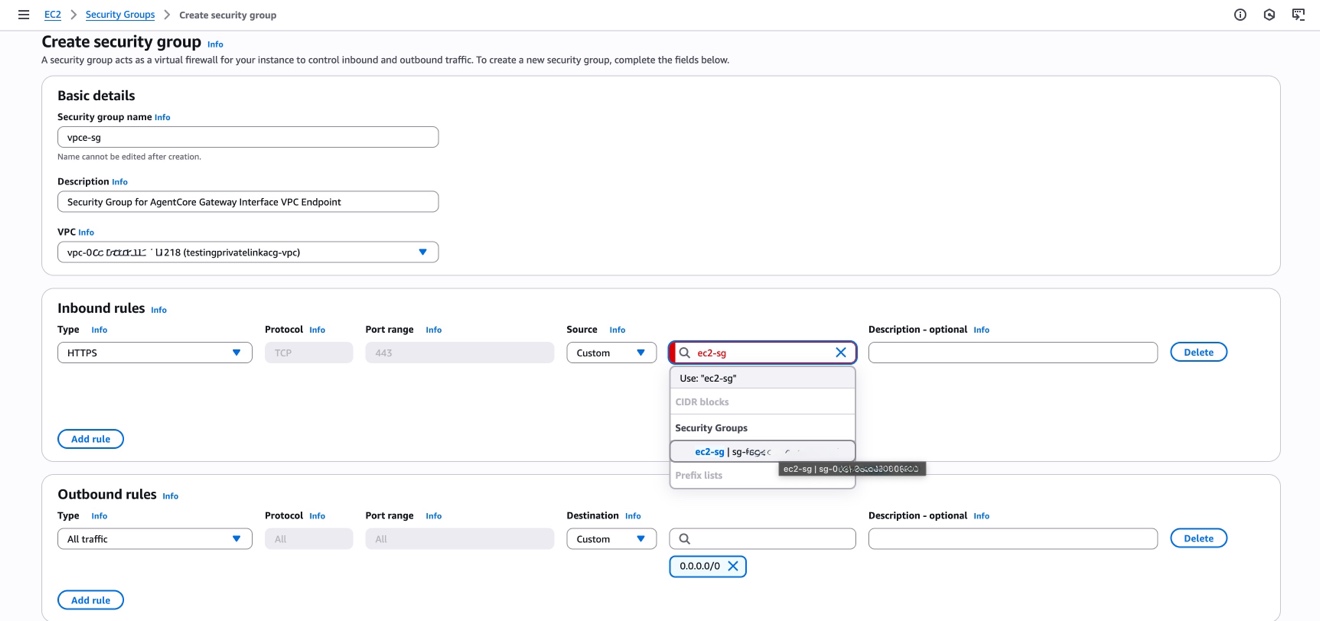
Create a safety group for the interface VPC endpoint
To create a safety group for the interface VPC endpoint, comply with these steps:
Create a second safety group named vpce-agentcore-sg that will probably be hooked up to the AgentCore Gateway interface VPC endpoint utilizing comparable steps to the previous directions and deciding on the identical VPC. For this safety group, configure the next guidelines to allow safe and restricted entry:
- Inbound guidelines – Permit HTTPS (port 443) for safe communication to the AgentCore Gateway
- Supply – Choose the EC2 safety group (
ec2-agent-sg) you created within the previous part to permit visitors solely from licensed agent situations - Outbound guidelines – Go away as default (all visitors allowed) to help response visitors
This safety group configuration implements the precept of least privilege by ensuring solely EC2 situations with the agent safety group can entry the VPC endpoint whereas blocking unauthorized entry from different sources within the VPC. These steps are illustrated by the next screenshot.
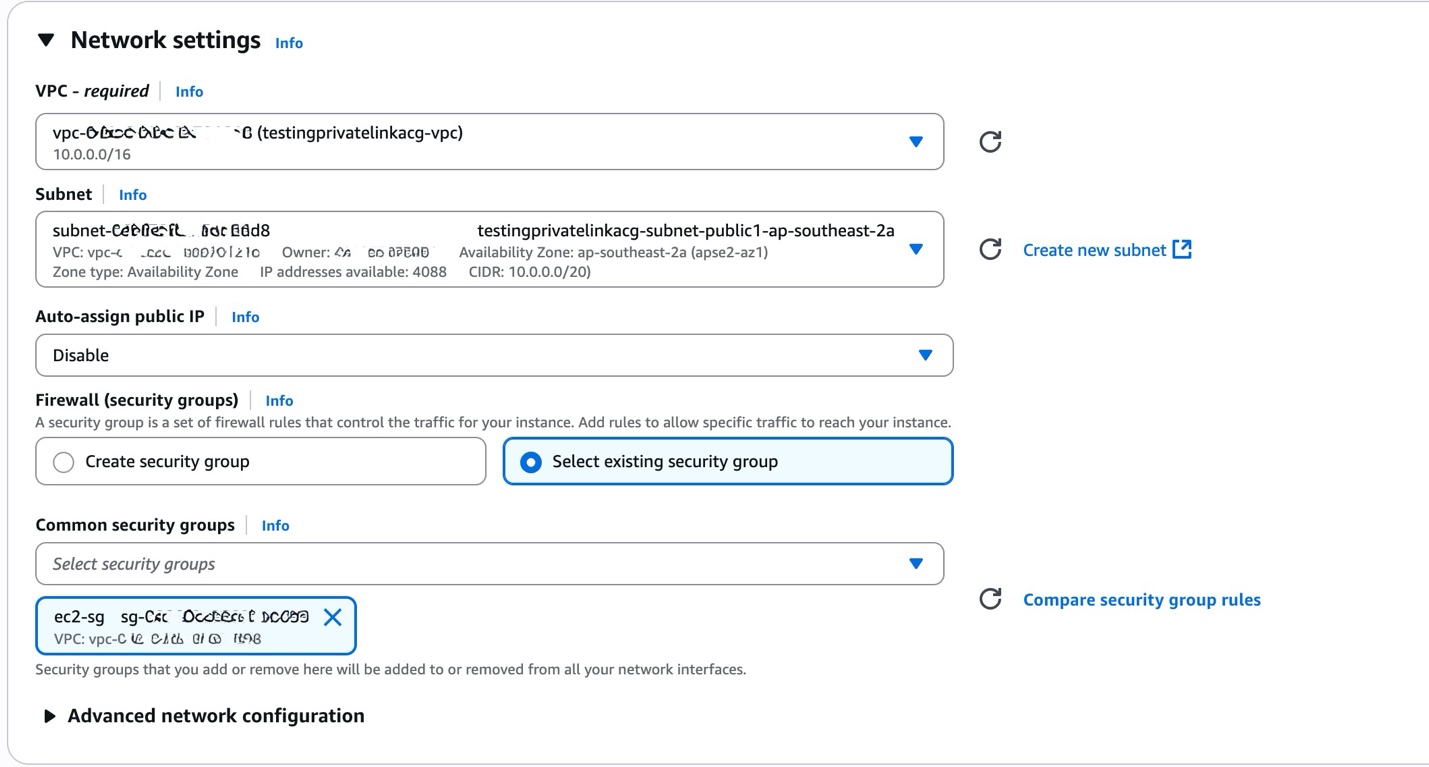
Provision an EC2 occasion throughout the VPC
Provision an EC2 occasion in the identical VPC and choose an acceptable Availability Zone in your workload necessities. Configure the occasion with the community settings proven within the following checklist, ensuring you choose the identical VPC and observe the chosen subnet for VPC endpoint configuration:
- VPC – Choose your goal VPC
- Subnet – Select a personal subnet for enhanced safety (observe this subnet for VPC endpoint configuration)
- Safety group – Connect the EC2 safety group (
ec2-agent-sg) you created within the earlier steps - IAM position – Configure an IAM position with essential permissions for Amazon Bedrock and AgentCore Gateway entry
- Occasion kind – Select an acceptable occasion kind based mostly in your agent workload necessities
Keep in mind the chosen subnet since you’ll must configure the VPC endpoint in the identical subnet to facilitate optimum community routing and minimal latency. These configurations are proven within the following screenshot.
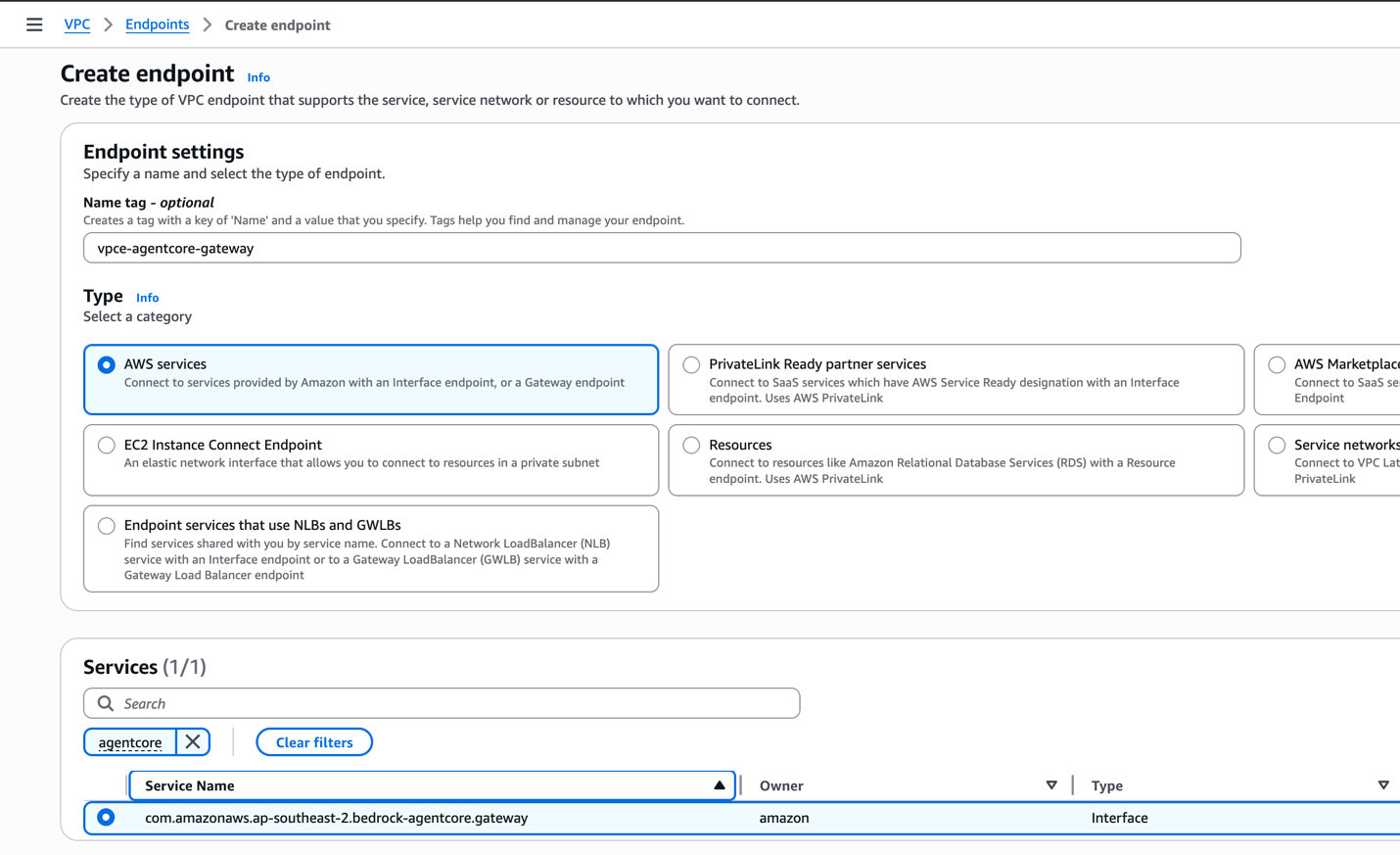
Create an interface VPC endpoint
Create an interface VPC endpoint utilizing Amazon Digital Non-public Cloud (Amazon VPC) that routinely makes use of AWS PrivateLink expertise, enabling safe communication out of your EC2 occasion to AgentCore Gateway with out traversing the general public web. Observe these steps:
- Navigate to the Amazon VPC console and select Endpoints within the navigation pane beneath the PrivateLink and Lattice part.
- Select Create endpoint.
- For Identify tag, enter a descriptive title (for instance,
vpce-agentcore-gateway). - For Service class, select AWS providers.
- For Providers, seek for and select
com.amazonaws.<area>.bedrock-agentcore.gateway(substitute<area>together with your precise AWS Area).
These settings are proven within the following screenshot.
- Set the VPC to the identical VPC you’ve been working with all through this setup.
- Choose Allow DNS title to permit entry to the AgentCore Gateway utilizing its default area title, which simplifies software configuration and maintains compatibility with present code.
- Specify the subnet the place the EC2 occasion is working to take care of optimum community routing and minimal latency, as proven within the following screenshot.
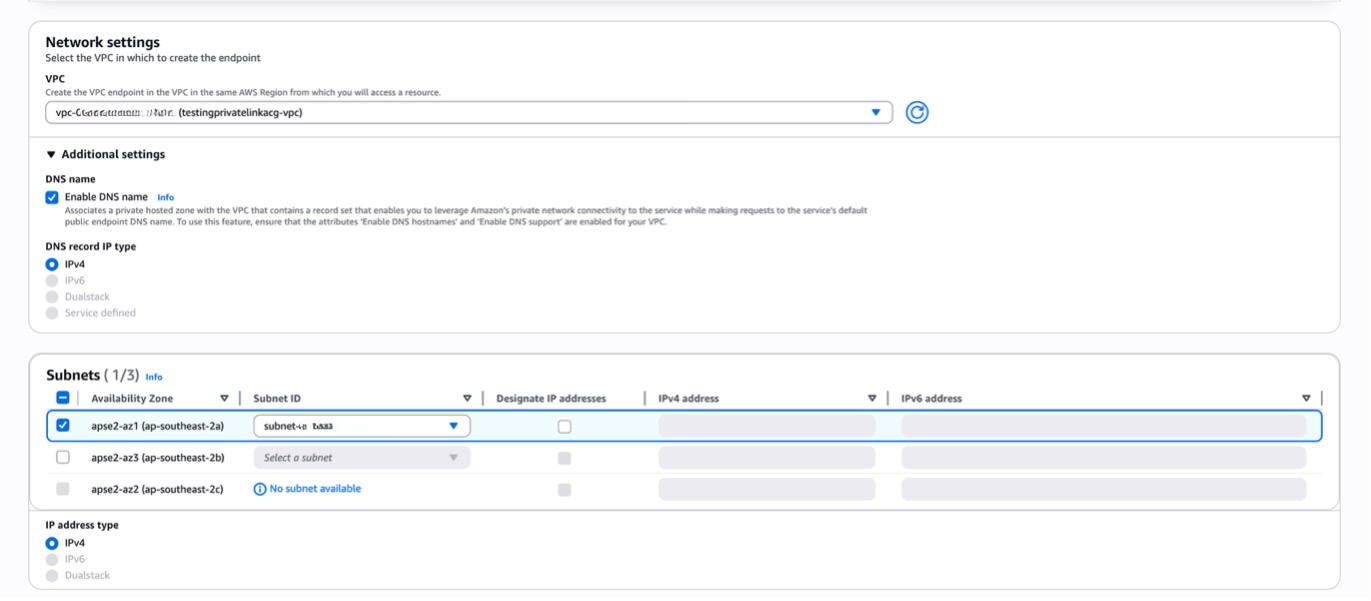
- Set the safety group to the VPC endpoint safety group (
vpce-agentcore-sg) you created earlier to manage entry to the endpoint. - For preliminary testing, depart the coverage set to Full entry to permit brokers inside your VPC to speak with AgentCore Gateway in your AWS account. In manufacturing environments, implement extra restrictive insurance policies based mostly on the precept of least privilege.
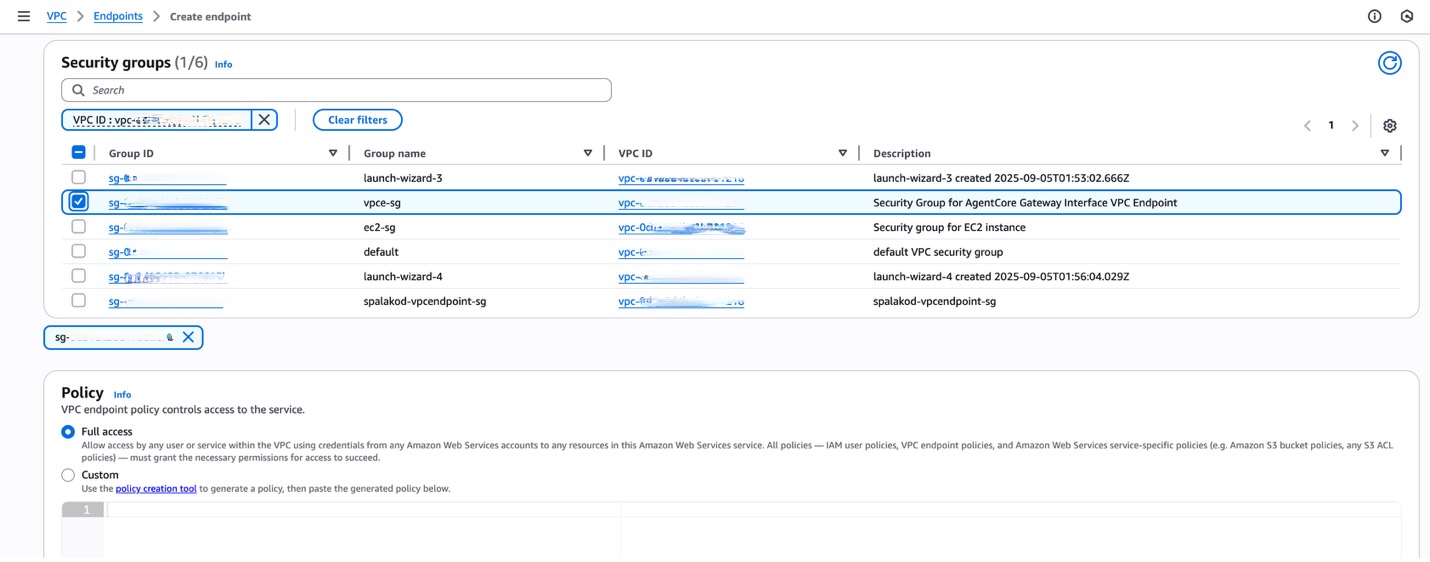
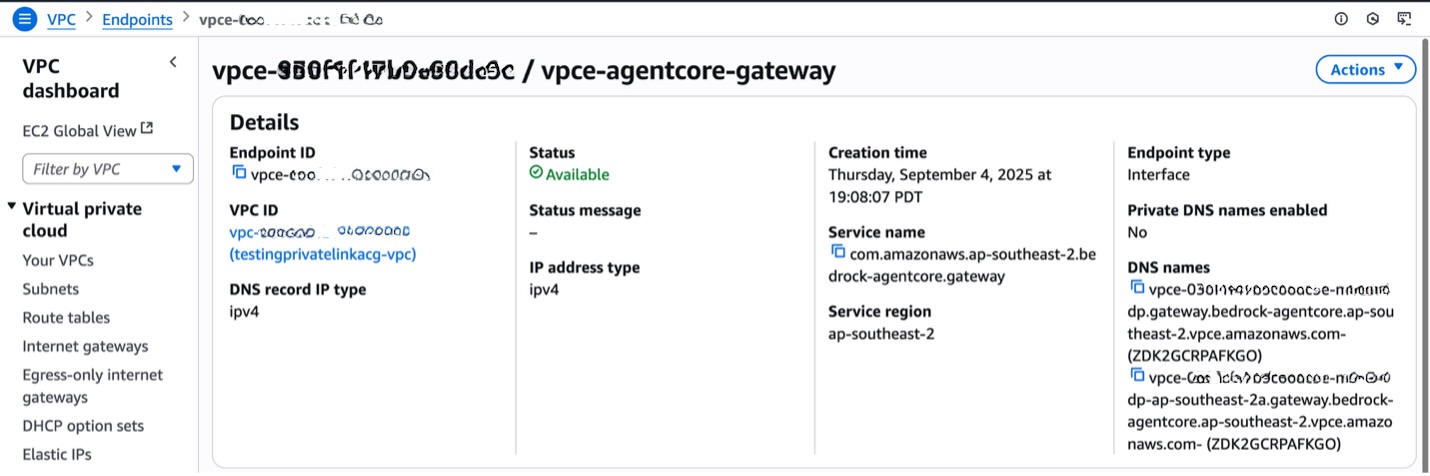
After you create the endpoint, it’ll take roughly 2–5 minutes to turn out to be obtainable. You may monitor the standing on the Amazon VPC console, and when it exhibits as Accessible, you’ll be able to proceed with testing the connection.
Take a look at the connection
Log in to the EC2 occasion to carry out following the checks.
Test visitors movement over an interface VPC endpoint
To substantiate the visitors movement by way of the Amazon Bedrock AgentCore Gateway endpoint, check the IP address of the source resource that connects to the AgentCore Gateway endpoint. While you arrange an interface VPC endpoint, AWS deploys an elastic community interface with a personal IP deal with within the subnet. This deployment permits communication with AgentCore Gateway from sources throughout the Amazon VPC and on-premises sources that connect with the interface VPC endpoint by way of AWS Direct Join or AWS Website-to-Website VPN. It additionally permits communication with sources in different Amazon VPC endpoints once you use centralized interface VPC endpoint structure patterns.
Test whether or not you turned on non-public DNS for the AgentCore Gateway endpoint. Should you activate non-public DNS, then AgentCore Gateway endpoints resolve to the non-public endpoint IP addresses. For AgentCore Gateway, enabling non-public DNS means your brokers can proceed utilizing the usual gateway endpoint URL whereas benefiting from non-public community routing by way of the VPC endpoint.
Earlier than VPC interface endpoint, as proven within the following instance, the DNS resolves to a public IP deal with for AgentCore Gateway endpoint:
After VPC interface endpoint creation with non-public DNS decision, as proven within the following instance, the DNS resolves to personal IP deal with from the CIDR vary of the subnet of the VPC during which the VPC endpoint was created.
When you choose Allow DNS title for AgentCore Gateway VPC interface endpoints, by default AWS activates the Allow non-public DNS just for inbound endpoints choice.
Non-public DNS enabled (cURL) (beneficial)
When non-public DNS is enabled, your functions can seamlessly use the usual gateway URL endpoint within the format https://{gateway-id}.gateway.bedrock-agentcore.{area}.amazonaws.com whereas visitors routinely routes by way of the VPC endpoint.
The next is a pattern cURL request to be executed from a useful resource throughout the VPC. The command sends a JSON-RPC POST request to retrieve obtainable instruments from the AgentCore Gateway:
This cURL command sends a JSON-RPC 2.0 POST request to the AgentCore Gateway MCP endpoint to retrieve a listing of obtainable instruments. It makes use of bearer token authentication and contains response headers within the output, calling the instruments/checklist methodology to find what instruments are accessible by way of the gateway.
Non-public DNS disabled (Python)
When Non-public DNS is disabled, you’ll be able to’t entry the gateway instantly by way of the usual AgentCore Gateway endpoint. As an alternative, you could route visitors by way of the VPC DNS title proven within the following screenshot and embody the unique gateway area title within the Host header.
The next steps beneath stroll by way of executing a Python script that makes use of the Host header:
- Entry your EC2 occasion. Log in to your EC2 occasion that has entry to the VPC endpoint.
- Configure the required surroundings variables for the connection:
- GATEWAY_URL – The VPC endpoint URL used to entry the AgentCore Gateway by way of your non-public community connection
- TOKEN – Your authentication bearer token for accessing the gateway
- GATEWAY_HOST – The unique AgentCore Gateway area title that have to be included within the Host header when Non-public DNS is disabled
For instance:
- Create and execute the check script.
- Copy the next Python code right into a file named agent.py. This code checks the AgentCore Gateway workflow by discovering obtainable instruments, making a Strands Agent with the instruments, after which testing each conversational interactions (instrument itemizing and climate queries) and direct MCP instrument calls. Copy the code:
- Invoke the script utilizing the next command:
python3 agent.py
Superior configuration: VPC endpoint entry insurance policies
A VPC endpoint coverage is a resource-based coverage that controls entry to AWS providers by way of the endpoint. Not like identity-based insurance policies, endpoint insurance policies present a further layer of entry management on the community degree. You may configure entry insurance policies for AgentCore Gateway VPC endpoints with particular issues.When creating endpoint insurance policies for AgentCore Gateway, think about these key components:
- Principal configuration – The
Principaldiscipline can’t be modified as a result of AgentCore Gateway doesn’t use IAM for authentication. Authentication is dealt with by way of bearer tokens slightly than IAM principals. - Useful resource specification – Clearly outline the
Useful resourcediscipline if you wish to limit entry to particular gateway endpoints. Use the complete Amazon Useful resource Identify (ARN) format to focus on explicit gateways inside your account as proven within the following pattern coverage construction. - Motion permissions – For the
Motiondiscipline, keep away from specifying management aircraft operations. Use a wildcard (*) to permit the required knowledge aircraft operations for gateway performance.
Here’s a pattern coverage construction:
When the VPC endpoint coverage blocks a request, you will notice error responses reminiscent of:
Coverage caching habits
AgentCore Gateway implements a caching mechanism for entry insurance policies that introduces a delay of as much as quarter-hour earlier than coverage adjustments take impact. Though this caching considerably improves gateway efficiency, it signifies that coverage modifications won’t be instantly mirrored in entry controls. To work successfully with this habits, it’s best to permit a minimum of quarter-hour for coverage adjustments to completely propagate all through the system after making updates. When attainable, schedule coverage modifications throughout deliberate upkeep home windows to reduce operational affect. All the time check coverage adjustments in nonproduction environments earlier than making use of them to manufacturing gateways and issue within the caching delay when diagnosing access-related points to keep away from untimely troubleshooting efforts.
Superior patterns
In a shared gateway, a number of brokers sample, a number of brokers from completely different providers entry a single centralized gateway by way of a shared VPC endpoint, simplifying community structure whereas sustaining safety by way of token-based authentication. This sample is illustrated within the following diagram.
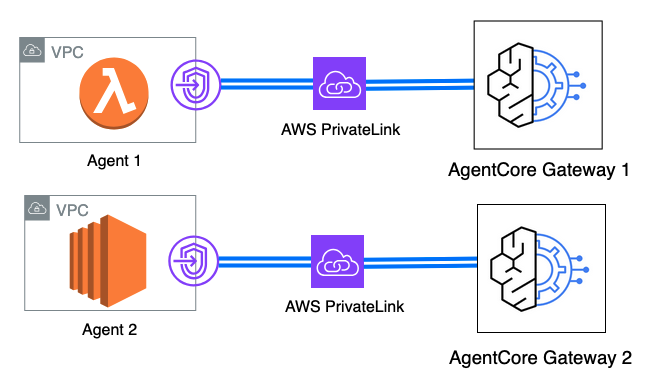
In a multi-gateway, multi-agent sample, which is proven within the following diagram, a number of brokers throughout completely different functions entry a number of specialised gateways by way of devoted VPC endpoints, offering most safety isolation with entry management per gateway.
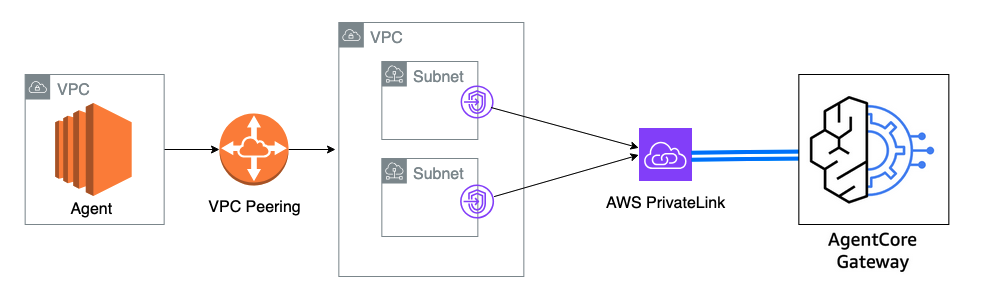
In a cross-VPC gateway entry sample, proven within the following diagram, brokers in a number of VPCs can entry AgentCore Gateway by way of VPC peering or AWS Transit Gateway connections, permitting centralized gateway entry throughout community boundaries whereas sustaining isolation.
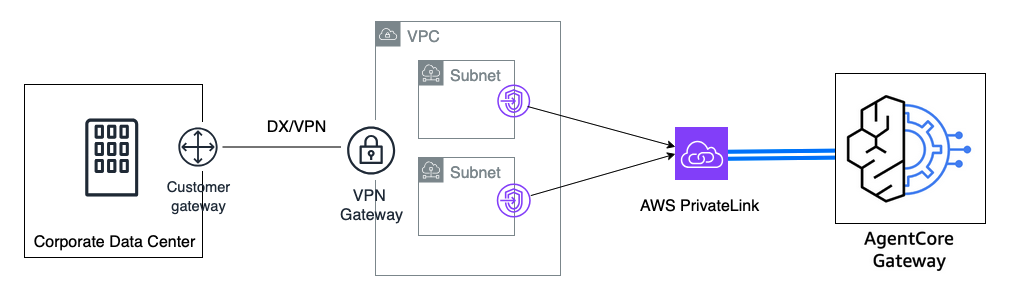
In a hybrid cloud gateway sample, on-premises brokers can entry cloud-based gateways by way of VPC endpoints with non-public DNS disabled, enabling hybrid cloud deployments by way of Direct Join or VPN connections. The next diagram illustrates this sample.
Clear up
To keep away from ongoing prices and preserve good useful resource hygiene, clear up your sources by finishing the next steps so as:Delete the EC2 occasion:
- Navigate to the Amazon EC2 console and choose your check occasion
- Select Occasion state and Cease occasion, then watch for it to cease
- Select Occasion state and Terminate occasion to completely delete the occasion
Delete the VPC endpoint:
- Navigate to the Amazon VPC console and select Endpoints
- Choose the VPC endpoint (
vpce-agentcore-gateway) you created - Select Actions and Delete VPC endpoints
- Affirm the deletion
Delete the safety teams:
- Navigate to the Amazon EC2 console and select Safety teams
- Choose the EC2 safety group (
ec2-agent-sg) you created - Select Actions and Delete safety teams
- Repeat for the VPC endpoint safety group (
vpce-agentcore-sg)
Conclusion
On this submit, we demonstrated learn how to set up safe, non-public connectivity between VPC-hosted sources and Amazon Bedrock AgentCore Gateway utilizing VPC interface endpoints and AWS PrivateLink. This structure delivers complete advantages for enterprise agentic AI deployments by implementing networks which might be remoted from the web, offering enhanced safety by way of devoted non-public community paths. The answer implements a strong knowledge perimeter by way of VPC endpoint insurance policies, which create granular entry controls that set up strict knowledge boundaries round your AI sources. Moreover, the structure permits non-public connectivity to Gateway endpoints for on-premises environments, supporting distributed AI architectures that span cloud and on-premises infrastructure. For organizations deploying autonomous AI methods at scale, implementing VPC interface endpoints creates the safe networking basis essential for environment friendly agent operations whereas delivering diminished latency by way of optimized community paths. This enterprise-grade method helps allow your agentic AI functions to attain improved efficiency and diminished response instances whereas assembly safety and compliance necessities.
To study extra about implementing these patterns and greatest practices, go to the Amazon Bedrock documentation and AWS PrivateLink documentation for complete steering on AI deployments.
Concerning the authors
Dhawal Patel is a Principal Machine Studying Architect at Amazon Internet Providers (AWS). He has labored with organizations starting from giant enterprises to midsized startups on issues associated to distributed computing and AI. He focuses on deep studying, together with pure language processing (NLP) and laptop imaginative and prescient domains. He helps prospects obtain high-performance mannequin inference on Amazon SageMaker.
is a Principal Machine Studying Architect at Amazon Internet Providers (AWS). He has labored with organizations starting from giant enterprises to midsized startups on issues associated to distributed computing and AI. He focuses on deep studying, together with pure language processing (NLP) and laptop imaginative and prescient domains. He helps prospects obtain high-performance mannequin inference on Amazon SageMaker.
 Sindhura Palakodety is a Senior Options Architect at Amazon Internet Providers (AWS) and Single-Threaded Chief (STL) for ISV Generative AI, the place she is devoted to empowering prospects in growing enterprise-scale, Nicely-Architected options. She makes a speciality of generative AI and knowledge analytics domains, enabling organizations to leverage revolutionary applied sciences for transformative enterprise outcomes.
Sindhura Palakodety is a Senior Options Architect at Amazon Internet Providers (AWS) and Single-Threaded Chief (STL) for ISV Generative AI, the place she is devoted to empowering prospects in growing enterprise-scale, Nicely-Architected options. She makes a speciality of generative AI and knowledge analytics domains, enabling organizations to leverage revolutionary applied sciences for transformative enterprise outcomes.
 Thomas Mathew Veppumthara is a Sr. Software program Engineer at Amazon Internet Providers (AWS) with Amazon Bedrock AgentCore. He has earlier generative AI management expertise in Amazon Bedrock Brokers and almost a decade of distributed methods experience throughout Amazon eCommerce Providers and Amazon Elastic Block Retailer (Amazon EBS). He holds a number of patents in distributed methods, storage, and generative AI applied sciences.
Thomas Mathew Veppumthara is a Sr. Software program Engineer at Amazon Internet Providers (AWS) with Amazon Bedrock AgentCore. He has earlier generative AI management expertise in Amazon Bedrock Brokers and almost a decade of distributed methods experience throughout Amazon eCommerce Providers and Amazon Elastic Block Retailer (Amazon EBS). He holds a number of patents in distributed methods, storage, and generative AI applied sciences.
 June Won is a Principal Product Supervisor with Amazon SageMaker JumpStart. He focuses on making basis fashions (FMs) simply discoverable and usable to assist prospects construct generative AI functions. His expertise at Amazon additionally contains cell buying functions and last-mile supply.
June Won is a Principal Product Supervisor with Amazon SageMaker JumpStart. He focuses on making basis fashions (FMs) simply discoverable and usable to assist prospects construct generative AI functions. His expertise at Amazon additionally contains cell buying functions and last-mile supply.




