AWS helps trusted id propagation, a function that enables AWS providers to securely propagate a person’s id throughout service boundaries. With trusted id propagation, you will have fine-grained entry controls based mostly on a bodily person’s id moderately than counting on IAM roles. This integration permits for the implementation of entry management via providers reminiscent of Amazon S3 Entry Grants and maintains detailed audit logs of person actions throughout supported AWS providers reminiscent of Amazon EMR. Moreover, it helps long-running person background classes for coaching jobs, so you possibly can sign off of your interactive ML utility whereas the background job continues to run.
Amazon SageMaker Studio now helps trusted id propagation, providing a strong answer for enterprises in search of to reinforce their ML system safety. By integrating trusted id propagation with SageMaker Studio, organizations can simplify entry administration by granting permissions to current AWS IAM Id Heart identities.
On this submit, we discover the right way to allow and use trusted id propagation in SageMaker Studio, demonstrating its advantages via sensible use instances and implementation pointers. We stroll via the setup course of, talk about key concerns, and showcase how this function can rework your group’s method to safety and entry controls.
Answer overview
On this part, we overview the structure for the proposed answer and the steps to allow trusted id propagation in your SageMaker Studio area.
The next diagram exhibits the interplay between the completely different elements that permit the person’s id to propagate from their id supplier and IAM Id Heart to downstream providers reminiscent of Amazon EMR and Amazon Athena.
With a trusted id propagation-enabled SageMaker Studio area, customers can entry information throughout supported AWS providers utilizing their finish person id and group membership, along with entry allowed by their area or person execution function. As well as, API calls from SageMaker Studio notebooks and supported AWS providers and Amazon SageMaker AI options log the person id in AWS CloudTrail. For an inventory of supported AWS providers and SageMaker AI options, see Trusted id propagation structure and compatibility. Within the following sections, we present the right way to allow trusted id propagation in your area.
This answer applies for SageMaker Studio domains arrange utilizing IAM Id Heart as the tactic of authentication. In case your area is ready up utilizing IAM, see Implement user-level entry management for multi-tenant ML platforms on Amazon SageMaker AI for greatest practices on managing and scaling entry management.
Conditions
To observe together with this submit, you could have the next:
- An AWS account with a company occasion of IAM Id Heart configured via AWS Organizations
- Administrator permissions (or elevated permissions permitting modification of IAM principals, and SageMaker administrator entry to create and replace domains)
Create or replace the SageMaker execution function
For trusted id propagation to work, the SageMaker execution function (area and person profile execution function), ought to permit the sts:SetContext permissions, along with sts:AssumeRole, in its belief coverage. For a brand new SageMaker AI area, create a site execution function by following the directions in Create execution function. For current domains, observe the directions in Get your execution function to seek out the person or area’s execution function.
Subsequent, to replace the belief coverage for the function, full the next steps:
- Within the navigation pane of the IAM console, select Roles.
- Within the record of roles in your account, select the area or person execution function.
- On the Belief relationships tab, select Edit belief coverage.
- Replace the belief coverage with the next assertion:
- Select Replace coverage to save lots of your modifications.
Trusted id propagation solely works for personal areas on the time of launch.
Create a SageMaker AI area with trusted id propagation enabled
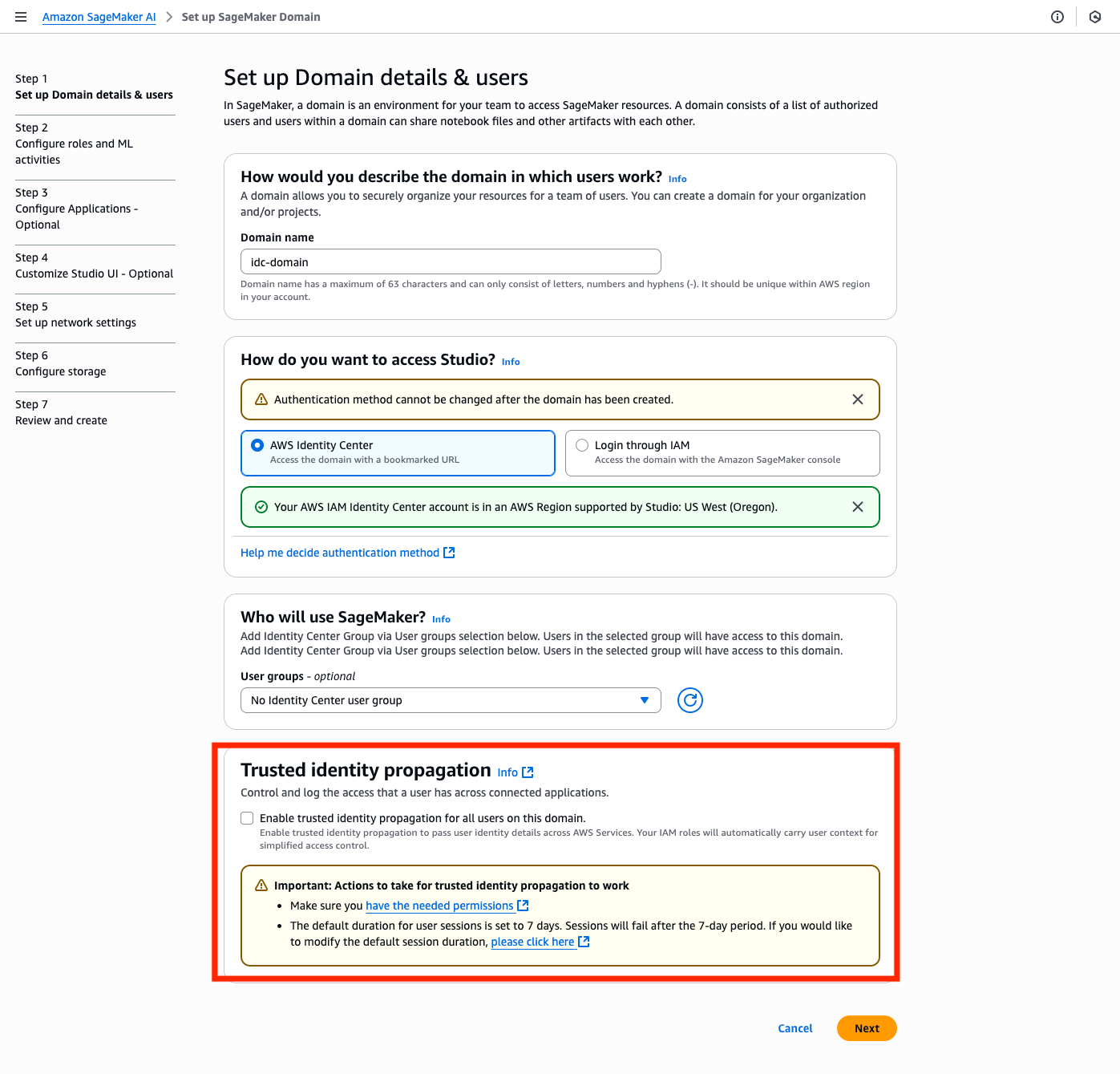
SageMaker AI domains utilizing IAM Id Heart for authentication can solely be arrange in the identical AWS Area because the IAM Id Heart occasion. To create a brand new SageMaker area, observe the steps in Use customized setup for Amazon SageMaker AI. For Trusted id propagation, choose Allow trusted id propagation for all customers on this area, and proceed with the remainder of the setup to create a site and assign customers and teams, selecting the function you created within the earlier step.
Replace an current SageMaker AI area
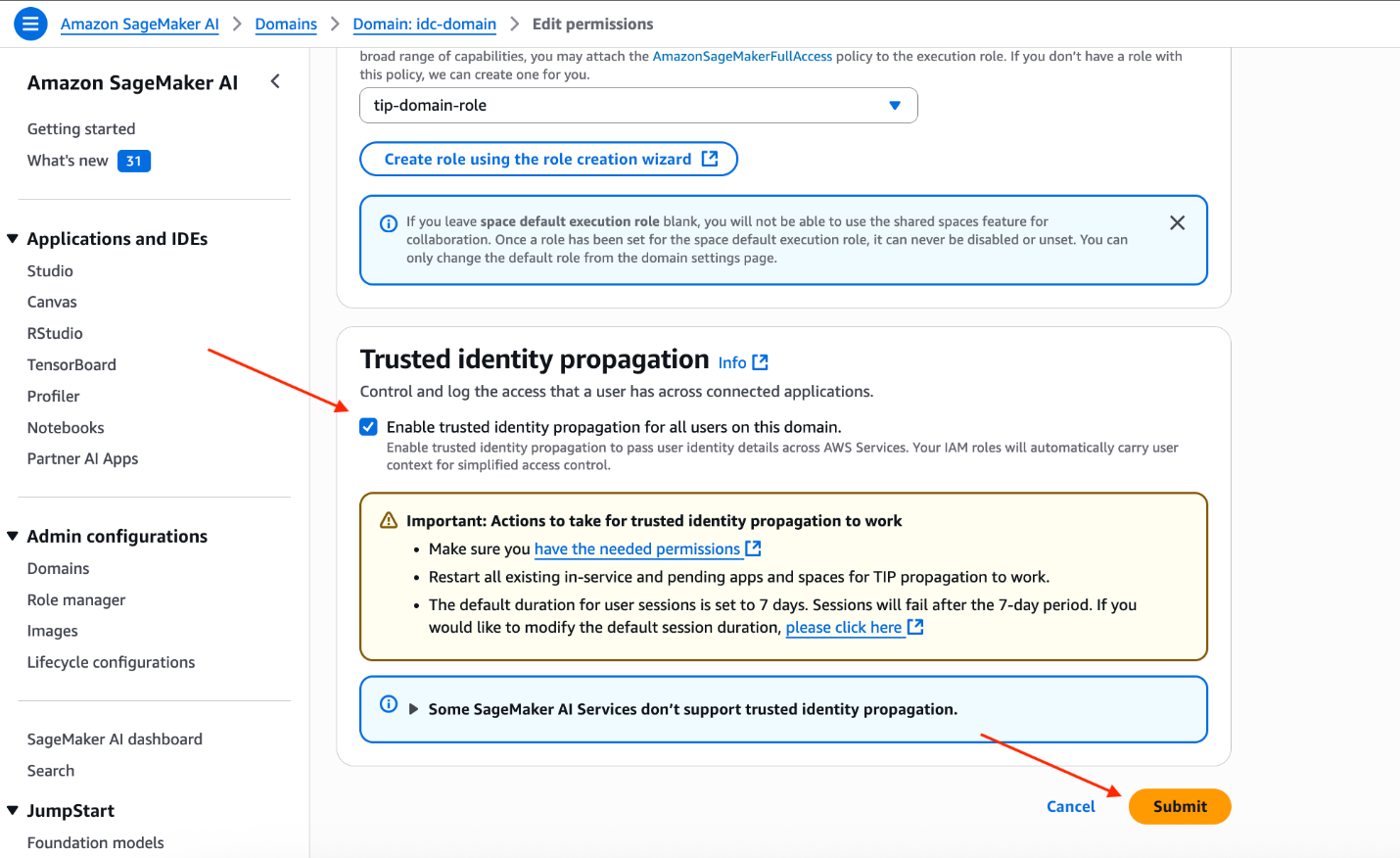
It’s also possible to replace your current SageMaker AI area to allow trusted id propagation. You’ll be able to allow trusted id propagation even whereas the area or person has energetic SageMaker Studio functions. Nonetheless, for the modifications to be utilized, the energetic functions have to be restarted. You should utilize the EffectiveTrustedIdentityPropagationStatus discipline within the response to the DescribeApp API for operating functions to find out if the appliance has trusted id propagation enabled.
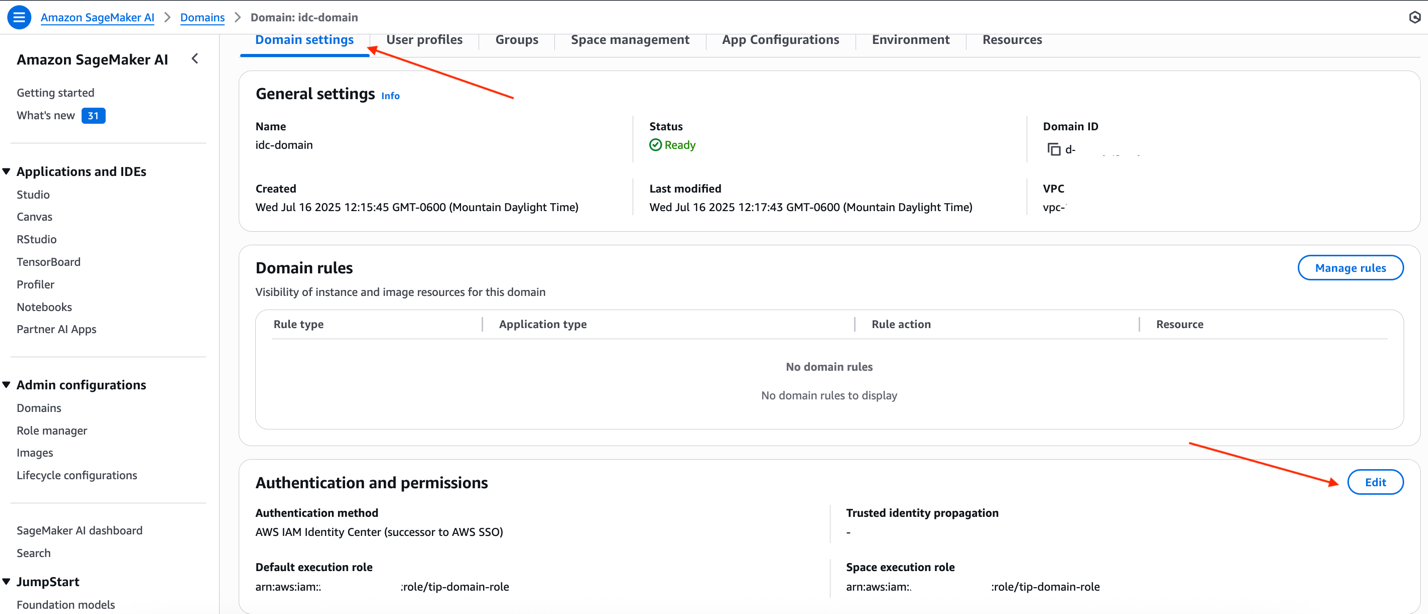
To allow trusted id propagation for the area utilizing the SageMaker AI console, select Edit below Authentication and permissions on the Area settings tab.
For Trusted id propagation, choose Allow trusted id propagation for all customers on this area, and select Submit to save lots of the modifications.
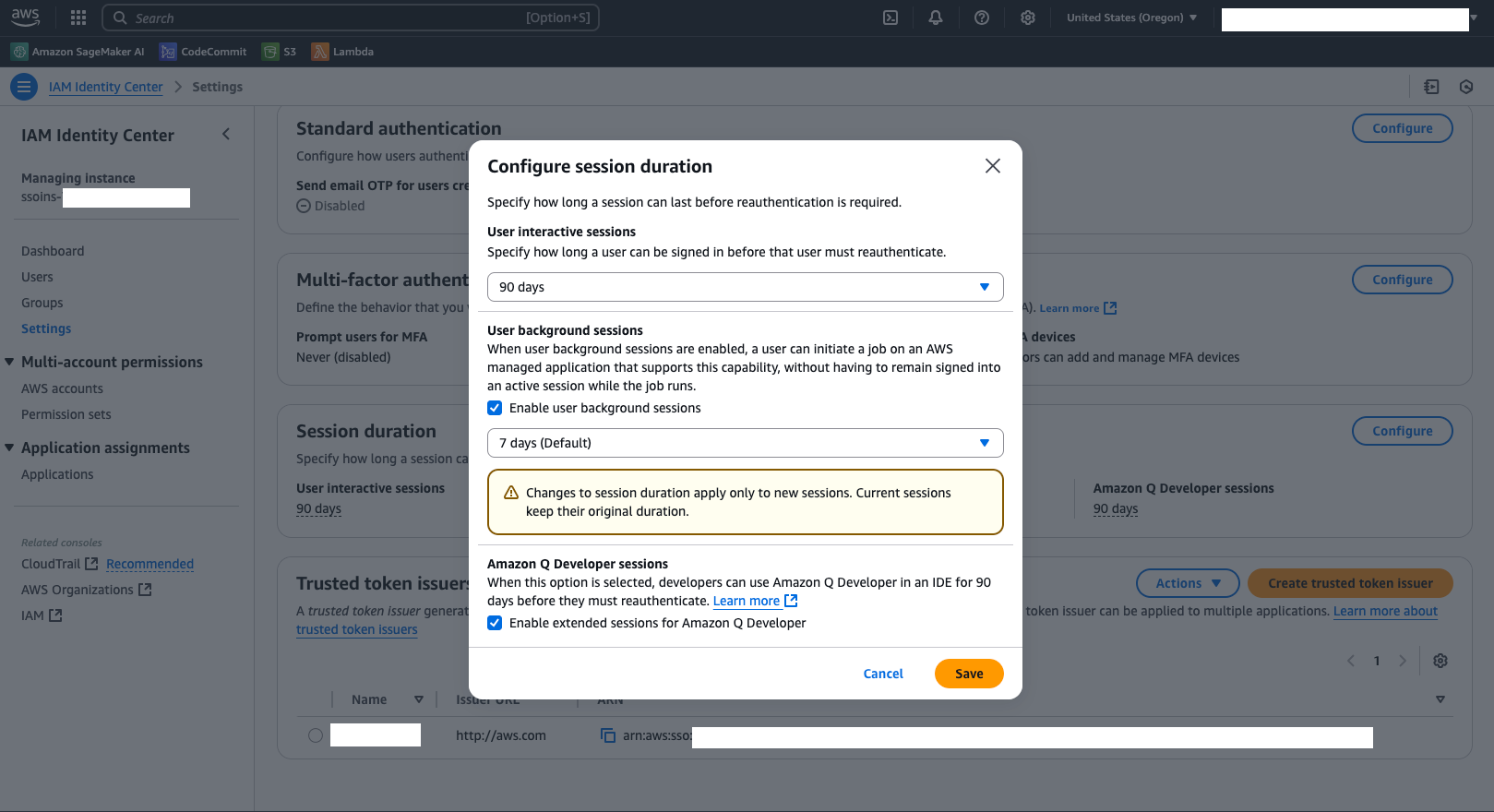
(Non-obligatory) Replace person background session configuration in IAM Id Heart
IAM Id Heart now helps operating person background classes, and the session period is ready by default to 7 days. With background classes, customers can launch long-running SageMaker coaching jobs that assume the person’s id context together with the SageMaker execution function. As an administrator, you possibly can allow or disable person background classes, and modify the session period for person background classes. As of the time of writing, the utmost session period which you could set for person background classes is 90 days. The person’s session is stopped on the finish of the desired period, and consequently, the coaching job can even fail on the finish of the session period.
To disable or replace the session period, navigate to the IAM Id Heart console, select Settings within the navigation pane, and select Configure below Session period.
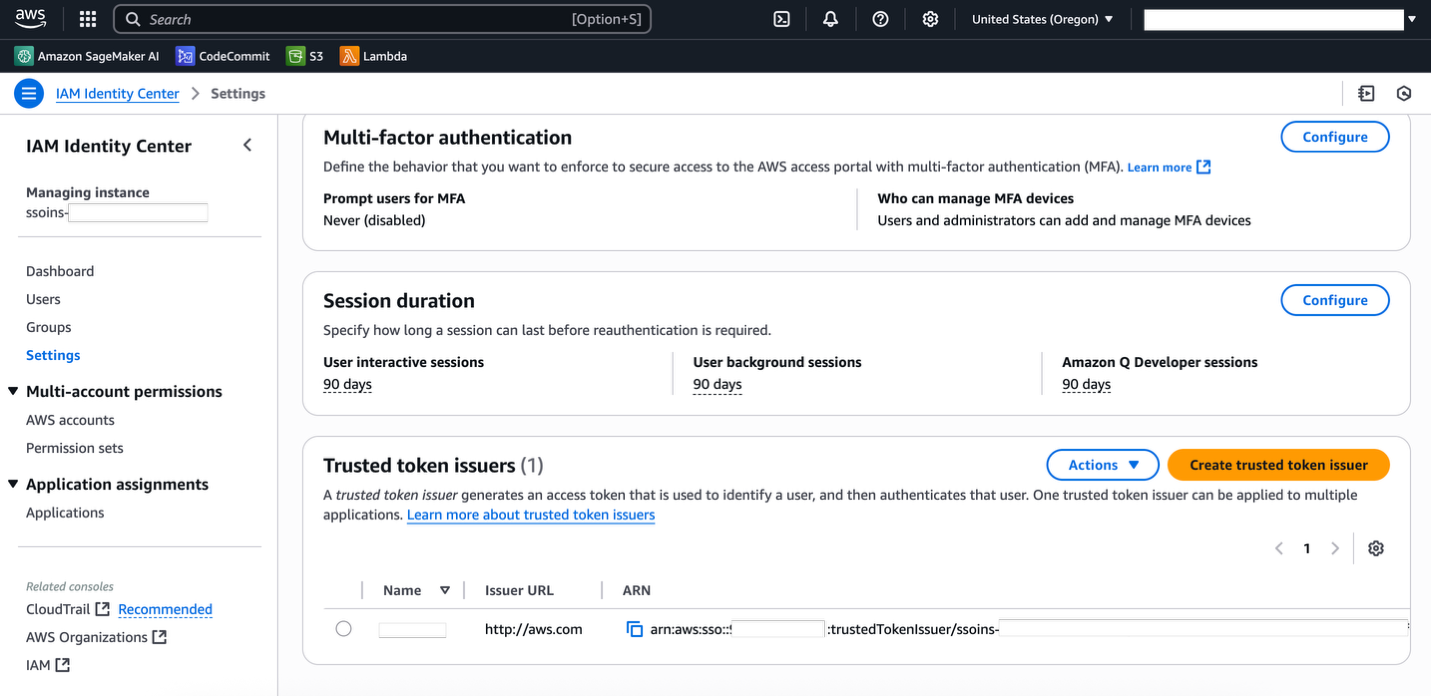
For Consumer background classes, choose Allow person background classes and use the dropdown to vary the session period. If person background classes are disabled, the person have to be logged in at some stage in the coaching job; in any other case, the coaching job will fail as soon as the person logs out. Updating this configuration doesn’t have an effect on present operating classes and solely applies to newly created person background classes. Select Save to save lots of your settings.
Use instances
Think about you’re an enterprise with a whole lot and even hundreds of customers, every requiring various ranges of entry to information throughout a number of groups. You’re answerable for sustaining an AI/ML system on SageMaker AI and managing entry permissions throughout numerous information sources reminiscent of Amazon Easy Storage Service (Amazon S3), Amazon Redshift, and AWS Lake Formation. Historically, this has concerned sustaining complicated IAM insurance policies for customers, providers, and assets, together with bucket insurance policies the place relevant. This method will not be solely tedious but in addition makes it difficult to trace and audit information entry with out sustaining a separate function for every person.
That is exactly the situation that trusted id propagation goals to deal with. With trusted id propagation assist, now you can preserve service-specific roles with minimal permissions, reminiscent of s3:GetDataAccess or LakeFormation:GetDataAccess, together with further permissions to start out jobs, view job statuses, and carry out different crucial duties. For information entry, you possibly can assign fine-grained insurance policies on to particular person customers. As an example, Jane may need learn entry to buyer information and full entry to gross sales and pricing information, whereas Laura may solely have learn entry to gross sales tendencies. Each Jane and Laura can assume the identical SageMaker AI function to entry their SageMaker Studio functions, whereas sustaining separate information entry permissions based mostly on their particular person identities.Within the following sections, we discover how this may be achieved for frequent use instances, demonstrating the ability and suppleness of trusted id propagation in simplifying information entry administration whereas sustaining sturdy safety and auditability.
State of affairs 1: Experiment with Amazon S3 information in notebooks
S3 Entry Grants present a simplified strategy to handle information entry at scale. Not like conventional IAM roles and insurance policies that require an in depth data of IAM ideas, and frequent coverage updates as new assets are added, with S3 Entry Grants, you possibly can outline entry to information based mostly on acquainted database-like grants that robotically scale together with your information. This method considerably reduces the operational overhead of managing hundreds of IAM insurance policies and bucket insurance policies, and overcomes the constraints of IAM permissions, whereas strengthening safety via entry patterns. If you happen to don’t have S3 Entry Grants arrange, see Create an S3 Entry Grant occasion to get began. For detailed structure and use instances, it’s also possible to check with Scaling information entry with Amazon S3 Entry Grants. After you will have arrange S3 Entry Grants, you possibly can grant entry to your datasets to customers based mostly on their id in IAM Id Heart.
To make use of S3 Entry Grants from SageMaker Studio, replace the next IAM roles with insurance policies and belief insurance policies.
For the area or person execution function, add the next inline coverage:
Make sure that the S3 Entry Grants function’s belief coverage permits the sts:SetContext motion along with sts:AssumeRole. The next is a pattern belief coverage:
GetDataAccess API to return momentary credentials, and by assuming the momentary credentials to learn or write to their prefixes. For instance, the next code exhibits the right way to use Boto3 to get momentary credentials and assume the credentials to get entry to Amazon S3 places which might be allowed via S3 Entry Grants:
State of affairs 2: Entry Lake Formation via Athena
Lake Formation supplies centralized governance and fine-grained entry management administration for information saved in Amazon S3 and metadata within the AWS Glue Knowledge Catalog. The Lake Formation permission mannequin operates along with IAM permissions, providing granular controls on the database, desk, column, row, and cell ranges. This dual-layer safety mannequin supplies complete information governance whereas sustaining flexibility in entry patterns.
Knowledge ruled via Lake Formation will be accessed via numerous AWS analytics providers. On this situation, we display utilizing Athena, a serverless question engine that integrates seamlessly with Lake Formation’s permission mannequin. For different providers like Amazon EMR on EC2, be certain the useful resource is configured to assist trusted id propagation, together with establishing safety configurations and ensuring the EMR cluster is configured with IAM roles that assist trusted id propagation.
The next directions assume that you’ve got already arrange Lake Formation. If not, see Arrange AWS Lake Formation and observe the AWS Lake Formation tutorials to arrange Lake Formation and herald your information.
Full the next steps to entry your ruled information in trusted id propagation-enabled SageMaker Studio notebooks utilizing Athena:
- Combine Lake Formation with IAM Id Heart by following the directions in Integrating IAM Id Heart. At a excessive stage, this consists of creating an IAM function permitting creating and updating utility configurations in Lake Formation and IAM Id Heart, and offering the one sign-on (SSO) occasion ID.
- Grant permissions to the IAM Id Heart person to the related assets (database, desk, row or column) utilizing Lake Formation. See Granting permissions on Knowledge Catalog assets directions.
- Create an Athena workgroup that helps trusted id propagation by following directions in Create a workgroup and selecting IAM Id Heart as the tactic of authentication. Make sure that the person has entry to jot down to the question outcomes location supplied right here utilizing S3 Entry Grants, as a result of Athena makes use of entry grants by default when selecting IAM Id Heart because the authentication methodology.
- Replace the Athena workgroup’s IAM function with the next belief coverage (add
sts:SetContextto the present belief coverage). You will discover the IAM function by selecting the workgroup you created earlier and in search of Function title.
The setup is now full. Now you can launch SageMaker Studio utilizing an IAM Id Heart person, launch a JupyterLab or Code Editor utility, and question the database. See the next instance code to get began:
State of affairs 3: Create a coaching job supported with person background classes
For a trusted id propagation-enabled area, a person background session is a session that continues to run even when the end-user has logged out of their interactive session reminiscent of JupyterLab functions in SageMaker Studio. For instance, the person can provoke a coaching job from their SageMaker Studio area, and the job can run within the background for days or even weeks whatever the person’s exercise, and use the person’s id to entry information and log audit trails. In case your area doesn’t have trusted id propagation enabled, you possibly can proceed to run coaching jobs and processing jobs as earlier than; nonetheless, if trusted id propagation is enabled, be certain your person background session time is up to date to replicate the period of your coaching jobs, as a result of the default is ready robotically to 7 days. In case you have enabled person background classes, replace your SageMaker Studio area or person’s execution function with the next permissions to offer a seamless expertise for information scientists:
With this setup, a knowledge scientist can use an Amazon S3 location that they’ve entry to via S3 Entry Grants. SageMaker robotically seems for information entry utilizing S3 Entry Grants and falls again to the job’s IAM function in any other case. For instance, within the following SDK name to create the coaching job, the person supplies the S3 Amazon URI the place the info is saved, they’ve entry to it via S3 Entry Grants, they usually can run this job with out further setup:
(Non-obligatory) View and handle person background classes on IAM Id Heart
When coaching jobs are run as person background classes, you possibly can view these classes as person background classes on IAM Id Heart. The administrator can view an inventory of all person background classes and optionally cease a session if the person has left the staff, for instance. When the person background session is ended, the coaching job subsequently fails.
To view an inventory of all person background classes, on the IAM Id Heart console, select Customers and select the person you need view the person background classes for. Select the Energetic classes tab to view an inventory of classes. The person background session will be recognized by the Session kind column, which exhibits if the session is interactive or a person background session. The record additionally exhibits the job’s Amazon Useful resource Title (ARN) below the Utilized by column.
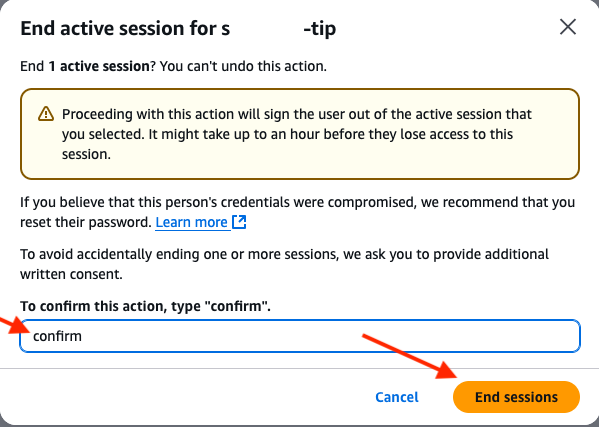
To finish a session, choose the session and select Finish classes.
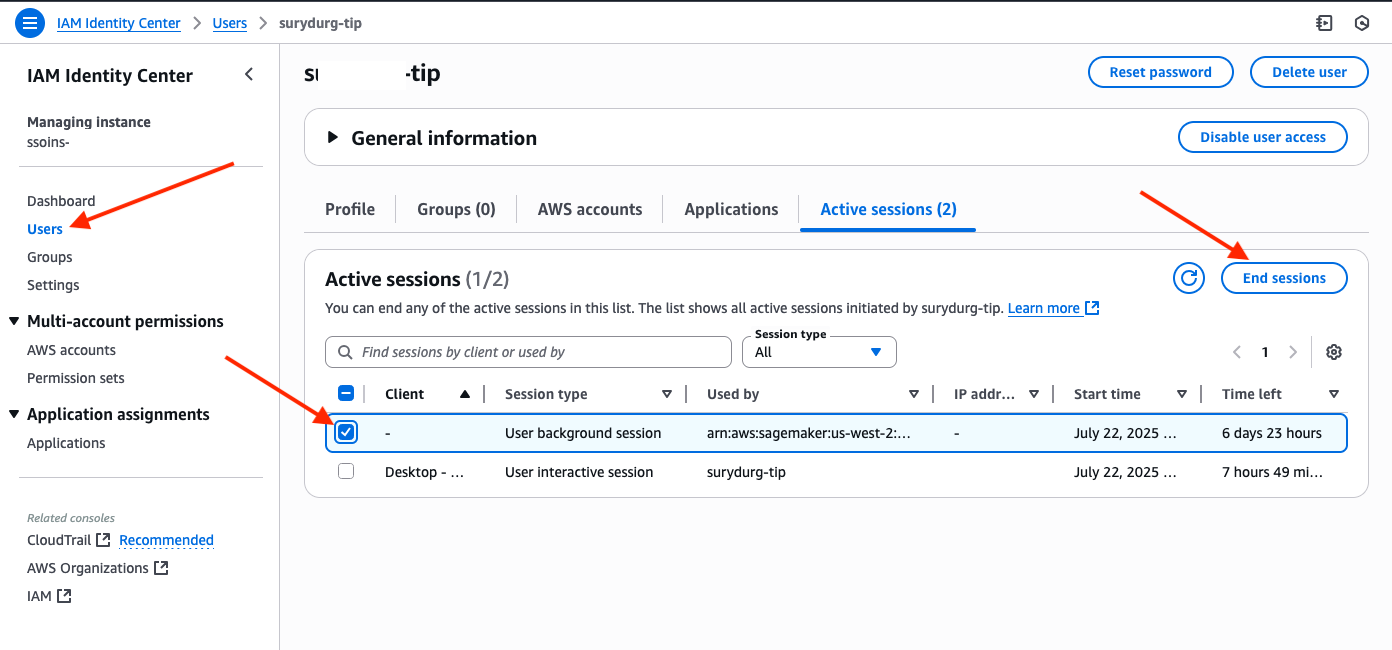
You can be prompted to substantiate the motion. Enter affirm to substantiate that you simply need to finish the session and select Finish classes to cease the person background session.
State of affairs 4: Auditing utilizing CloudTrail
After trusted id propagation is enabled in your area, now you can monitor the person that carried out particular actions via CloudTrail. To do this out, log in to SageMaker Studio, and create and open a JupyterLab area. Open a terminal and enter aws s3 ls to record the out there buckets in your Area.
On the CloudTrail console, select Occasion historical past within the navigation pane. Replace the Lookup attributes to Occasion title and within the search field, enter ListBuckets. You must see an inventory of occasions, as proven within the following screenshot (it’d take as much as 5 minutes for the logs to be out there in CloudTrail).
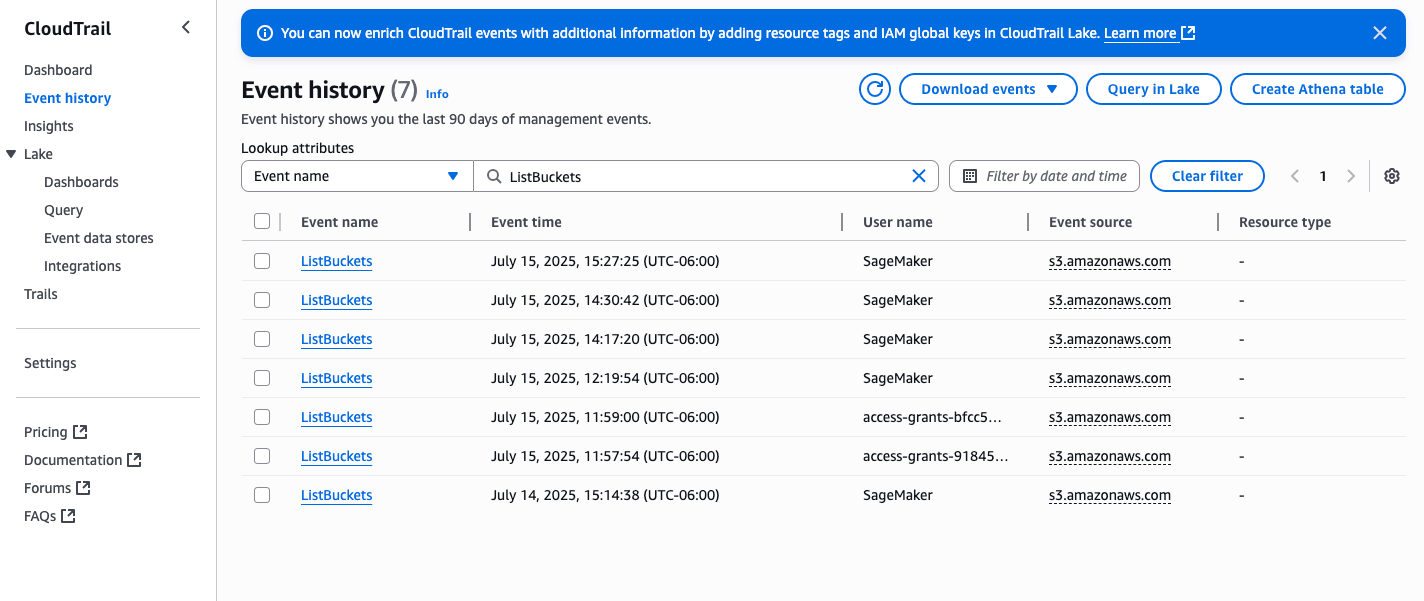
Select the occasion to view its particulars (confirm the person title is SageMaker if in case you have additionally listed buckets via the AWS console or APIs). Within the occasion particulars, it is best to be capable to see an extra discipline referred to as onBehalfOf that has the person’s id.
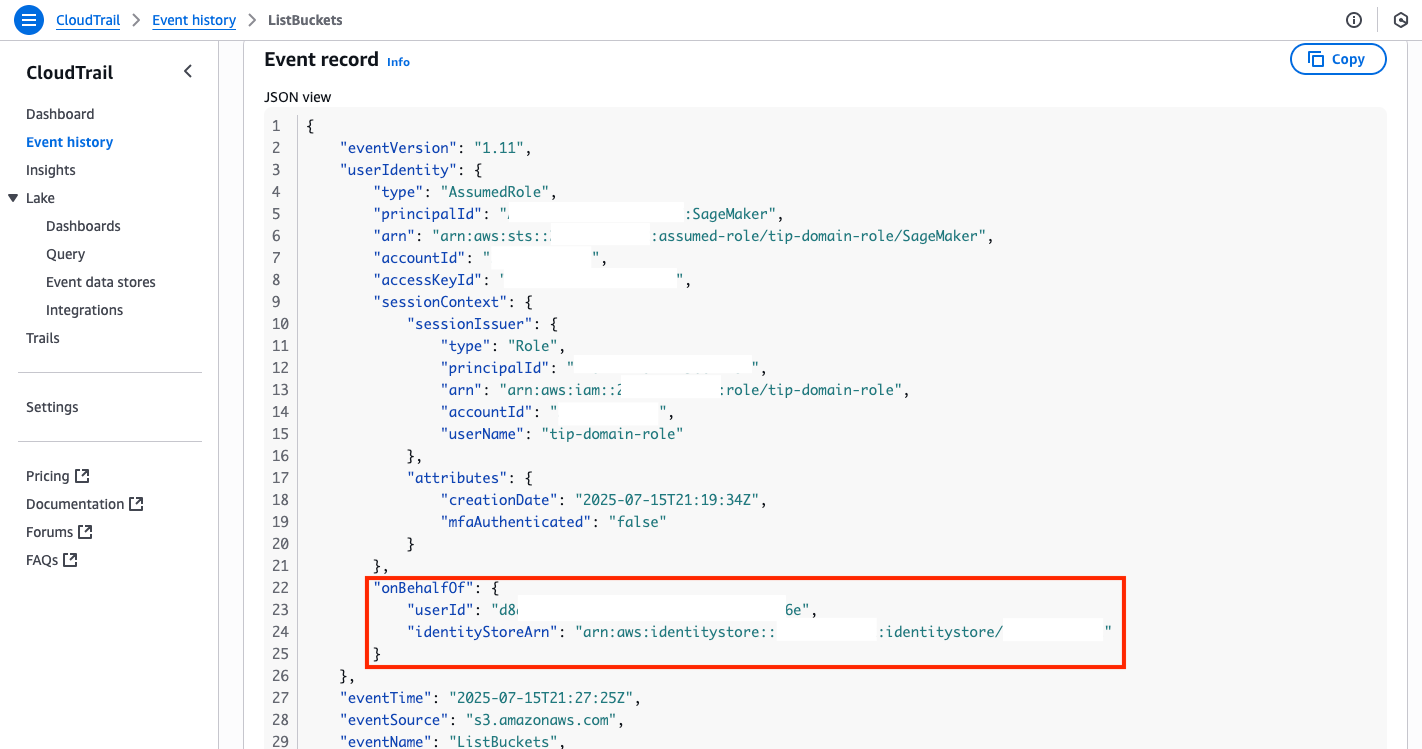
Supported providers and SageMaker AI options referred to as from a trusted id propagation-enabled SageMaker Studio area can have the OnBehalfOf discipline in CloudTrail.
Clear up
In case you have created a SageMaker Studio area for the needs of attempting out trusted id propagation, delete the area and its related Amazon Elastic File System (Amazon EFS) quantity to keep away from incurring further prices. Earlier than deleting a site, you could delete all of the customers and their related areas and functions. For detailed directions, see Cease and delete your Studio operating functions and areas.
If you happen to created a SageMaker coaching job, they’re ephemeral, and the compute is shut down robotically when the job is full.
Athena is a serverless analytics service that prices per question billing. No cleanup is important, however for greatest practices, delete the workgroup to take away unused assets.
Conclusion
On this submit, we confirmed you the right way to allow trusted id propagation for SageMaker AI domains that use IAM Id Heart because the mode of authentication. With trusted id propagation, directors can handle person authorization to different AWS providers via the person’s bodily id along with IAM roles. Directors can streamline permissions administration by sustaining a single area execution function and handle granular entry to different AWS providers and information sources via the person’s id. As well as, trusted id propagation helps auditing, so directors can monitor person exercise with out the necessity for managing a job for every person profile.
To study extra about enabling this function and its use instances, see Trusted id propagation use instances and Trusted id propagation with Studio. This submit coated a subset of supported functions; we encourage you to take a look at the documentation and select the providers that greatest serve your use case and share your suggestions!
Concerning the authors
 Amit Shyam Jaisinghani is a Software program Engineer on the SageMaker Studio staff at Amazon Net Providers, and he earned his Grasp’s diploma in Pc Science from Rochester Institute of Expertise. Since becoming a member of Amazon in 2019, he has constructed and enhanced a number of AWS providers, together with AWS WorkSpaces and Amazon SageMaker Studio. Outdoors of labor, he explores climbing trails, performs along with his two cats, Missy and Minnie, and enjoys taking part in Age of Empire.
Amit Shyam Jaisinghani is a Software program Engineer on the SageMaker Studio staff at Amazon Net Providers, and he earned his Grasp’s diploma in Pc Science from Rochester Institute of Expertise. Since becoming a member of Amazon in 2019, he has constructed and enhanced a number of AWS providers, together with AWS WorkSpaces and Amazon SageMaker Studio. Outdoors of labor, he explores climbing trails, performs along with his two cats, Missy and Minnie, and enjoys taking part in Age of Empire.
 Durga Sury is a Senior Options Architect at Amazon SageMaker, the place she helps enterprise prospects construct safe and scalable AI/ML programs. When she’s not architecting options, yow will discover her having fun with sunny walks along with her canine, immersing herself in homicide thriller books, or catching up on her favourite Netflix exhibits.
Durga Sury is a Senior Options Architect at Amazon SageMaker, the place she helps enterprise prospects construct safe and scalable AI/ML programs. When she’s not architecting options, yow will discover her having fun with sunny walks along with her canine, immersing herself in homicide thriller books, or catching up on her favourite Netflix exhibits.
 Khushboo Srivastava is a Senior Product Supervisor for Amazon SageMaker. She enjoys constructing merchandise that simplify machine studying workflows for patrons, and loves taking part in along with her 1-year previous daughter.
Khushboo Srivastava is a Senior Product Supervisor for Amazon SageMaker. She enjoys constructing merchandise that simplify machine studying workflows for patrons, and loves taking part in along with her 1-year previous daughter.
 Krishnan Manivannan is a Senior Software program Engineer at Amazon Net Providers and a founding member of the SageMaker AI API staff. He has 8 years of expertise within the structure and safety of large-scale machine studying providers. His specialties embrace API design, service scalability, id and entry administration, and inventing new approaches for constructing and working distributed programs. Krishnan has led a number of engineering efforts from design via international launch, delivering dependable and safe programs for patrons worldwide.
Krishnan Manivannan is a Senior Software program Engineer at Amazon Net Providers and a founding member of the SageMaker AI API staff. He has 8 years of expertise within the structure and safety of large-scale machine studying providers. His specialties embrace API design, service scalability, id and entry administration, and inventing new approaches for constructing and working distributed programs. Krishnan has led a number of engineering efforts from design via international launch, delivering dependable and safe programs for patrons worldwide.




