An intentional motion to obfuscate supply code refers to a change of programmatic logic right into a type that’s functionally an identical from a machine’s execution perspective, but extraordinarily tough for people to interpret. Though the conceptual premise is seemingly easy, this strategy holds a key place on the intersection of cybersecurity, mental property safety and strategic enterprise operations within the digital age.
Weight problems just isn’t a code, however the two are sometimes confused. Encryption signifies that knowledge can’t be absolutely readable till decrypted, however extra runtime processes should be required to revive usability. It’s primarily a type of an uneven data structure. It’s straightforward to grasp for machines and opaque to enemies.
Builders and know-how corporations make use of code obfuscation for quite a lot of interrelated functions. Primarily, it helps shield your personal logic from reverse engineering, thereby stopping theft of your mental property. Moreover, in contexts the place software program is deployed in hostile or semi-reliable environments, it can tamper with malformation and introduce important limitations to malformation. Moreover, obfuscation can obscure enterprise important algorithms, knowledge flows, or safety mechanisms, which will increase the price of cyber intrusion to grow to be an attacker.
Within the aggressive setting of contemporary know-how startups, the advantages of first driving are sometimes fleeting, and the codebase can characterize the whole monetisable property of an organization. Defending your supply code is greater than only a technical finest follow. That’s the accountability of the trustee. The usage of code obfuscation needs to be considered as one factor of a broader strategic perspective, together with secure improvement practices, mental property administration and mitigation of cybersecurity dangers.
Programmers will stop the supply code from being stolen (from the Latin phrase obfuscātus), and can tamper with and make it harder to guard beneficial or delicate details about the code’s performance.
In contrast to encryption, commentary makes knowledge solely tough for people to grasp. Obfuscating the supply code protects the code as knowledge stays machine-readable From cybercriminals With out including additional steps like decryption that may decelerate the execution time of this system.
In a extremely aggressive world Know-how-based startupsMental property is usually the very best worth asset owned by an organization. Implementing obfuscation strategies is an important step in defending IP from theft by rivals.
Why is the supply code so tough to guard?
Sometimes, beneficial knowledge and data are protected by limiting entry.
For instance, delicate consumer recordsdata are saved safe with password-protected, encrypted accounts which can be tough or not possible Violating criminals.
Nevertheless, since supply code is seen to folks utilizing this system, entry prevention strategies can’t be used to guard the code or the knowledge saved therein.
As an alternative, programmers can “faking” code through obfuscation, which appears meaningless to people, however nonetheless machine-readable. that is Prevents hackers By misusing code whereas making certain that this system runs as designed.

You need to use obfuscation software program to routinely apply numerous obfuscation strategies to sections of your code. Alternatively, the programmer can choose a portion of the info and obfuscate it manually.
The best way to obfuscate supply code and knowledge
There are numerous methods to obfuscate knowledge. To reinforce code safety, programmers can combine and match totally different strategies throughout the code, making it much more tough for hackers to learn.
Beneath we now have outlined among the extra widespread strategies for successfully obfuscating knowledge.
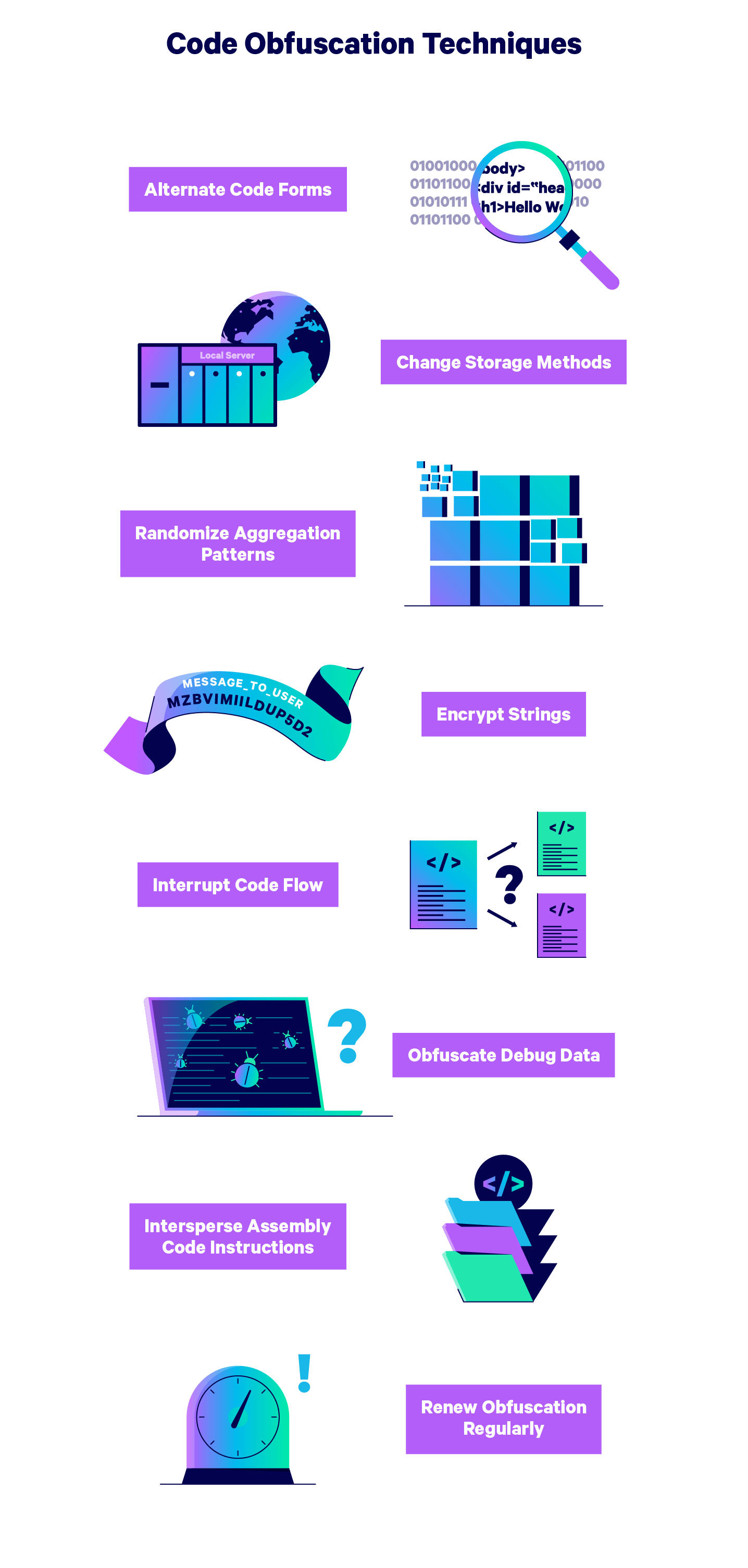
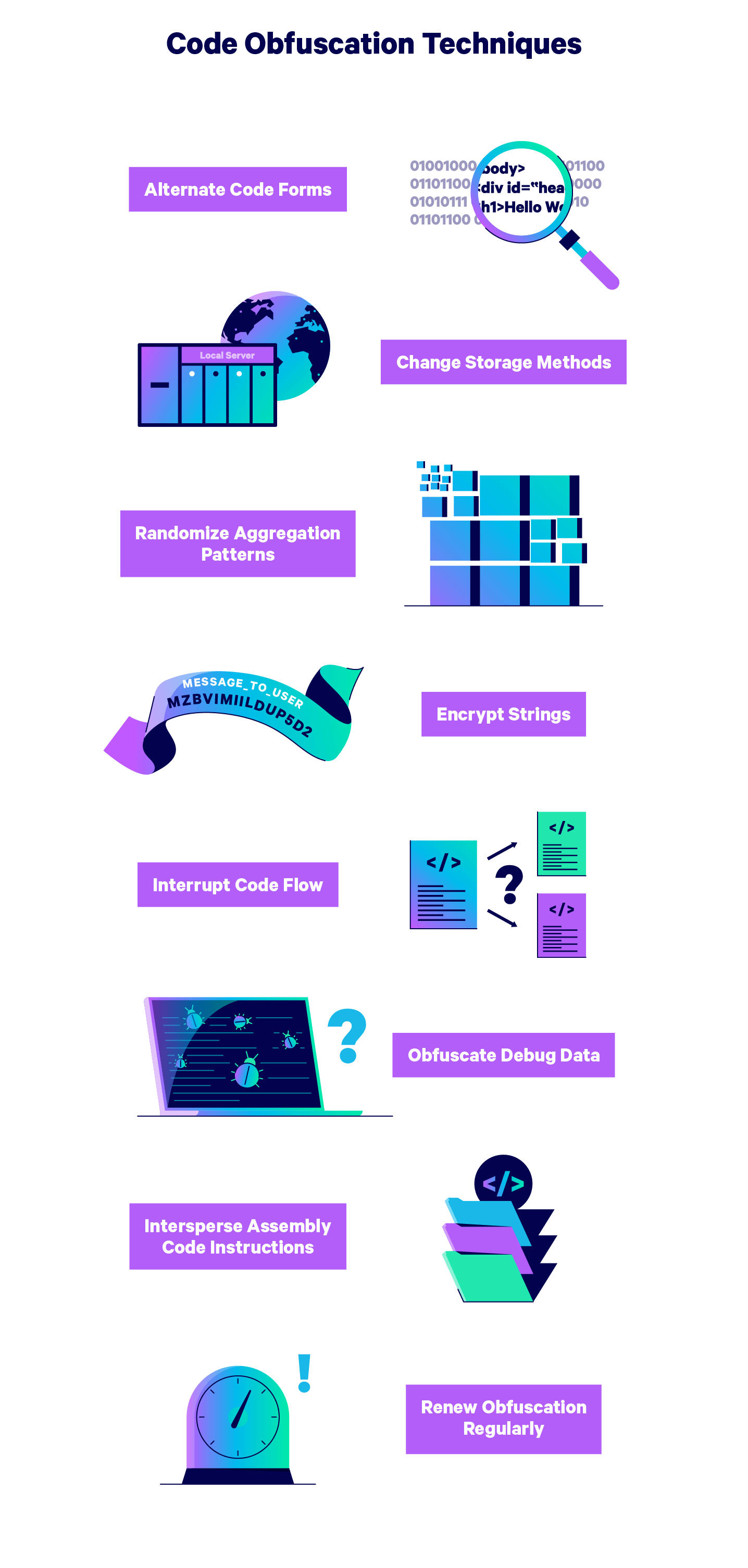
1. Alternate code type
Convert quick sections of code into totally different kinds all through this system, making deciphering harder with out affecting execution time.
For instance, you can translate a few of your code right into a binary language, or you can substitute the operate with a desk lookup of all of the values that the operate may generate.
2. Change the info storage methodology
By primarily “hiding” your knowledge utilizing quite a lot of reminiscence sorts and places, it makes your knowledge much more tough. It alternates between storing variables regionally and globally to cover how they work collectively.
You too can randomize the addresses the place the components of your code are situated, creating extra ranges of confusion, making studying your code harder.
3. Randomizes aggregation patterns
One other method to confuse hackers is to bundle the info into random sizes. For instance, you can unnecessarily cut up an array into many subarrays, complicated reverse engineering makes an attempt.
4. Encrypts a string
Though encryption just isn’t an efficient method to shield the whole supply code, it may be used as a part of the encryption course of with out delaying this system.
Create a hacker “blind spot” in your code by choosing and encrypting particular person keys, code strings, and different data.
5. Interrupt Code Move
Add pointless statements or “useless code” to your program to make it tough to know which components of your code comprise the precise knowledge.
You too can use dummy code to cover the paths by means of which program management is handed between sections of the codebase.
6. Delete debug knowledge
Debug data can be utilized by hackers to reverse engineer the supply code of this system, so it’s smart to obfuscate the debug data by altering the road numbers and file names.
Alternatively, you’ll be able to fully take away debugging data from this system.
7. Obfuscate meeting code
It focuses obfuscation efforts on meeting code, making reverse engineering significantly tough.
Many programmers desire to cover meeting codes inside different codes with a Russian nesting doll sample known as the “Leap within the Center” method.
8. Replace your obfuscation techniques usually
It adopts a schedule of obfuscation tactic updates and updates strategies used all through the code.
Change the components of the knowledge you hid and encrypted, altering the techniques of various components of your code.
Utilizing a number of techniques to completely obfuscate the supply code, and usually exhilarating obfuscation protects the startup’s IP from many of the potential hacking.
Nevertheless, safety measures can’t assure the security of your startup, so it is very important complement you. Cybersecurity Prevention Complete technical insurance coverage to incorporate Cyber accountability, Technical errors and omittedand Business Crime Insurance coverage To guard high-tech startups from all doable types of cyberattacks.
Defending programmer assault prevention efforts from worst-case eventualities will assist preserve your organization secure it doesn’t matter what occurs.
Try Embroker’s for extra data on the appropriate insurance policies for your small business Digital Insurance Platform.




